by Naief Budawelah
In our region (the Middle East) it is clear that in near future city traffic planning and managing would become one of the most critical aspects of cities management. The number of vehicles is increasing rapidly and today is in multiple folds compared to a decade ago. Most of these countries have an expanding road network but with a limited infrastructure. An article in Arab news stated that a 19 person is dying daily due to traffic accidents in Saudi Arabia, by 2014 the government decided to enforce traffic control and monitoring (19 die daily in KSA road accidents, 2013).
19 person is dying daily due to traffic accidents in Saudi Arabia
Recently traffic law enforcement authority; has been privatizing the traffic law enforcement, and awarded operators from the private sector license to operate as a traffic law enforcer in the different region within the country. Their duty ranged from deploying a fixed traffic violation camera (a fixed location) over intersections to monitor red light violation and in some street for a speed violation. Also, a mobile unit is used to perform the same task was used to minimize cost and increase efficiency.
The Operator is also responsible for collecting, verifying, validating, and violation registration with a national information center, which is a unique process requirement compared to other countries. The operator is responsible for buying and deploying, running the equipment and is paid back a percentage of the violation ticket value. A survey was conducted last year by these multiple operators and the common violations per day were around 35,000 violation per day (speeding and red-light violation).
the common violations per day were around 35,000 violation per day
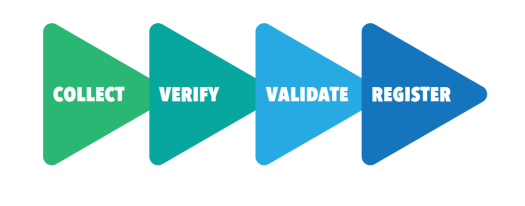
Figure 1. A High-Level Operator Business Process Flow
While the operators keep tweaking and accelerating the validation and verification processes (validation is a manual process; where an operator is required to validate the violation was a valid one, and the verification is also a manual process; to verify that the vehicle will not be reported as stolen, nor a police or an ambulance vehicle). However, the most important step in that process is the collection, which consists of deploying a fleet of mobile units to different streets and intersections.
Mobile units used for two reasons, the lack of internet connectivity in most of the sites that need monitoring, and reducing the cost due to a higher cost for the fixed locations and the need for a resource to collect the violation packages (images) manually.
In the daily operation, the Historical statistics is used to predict which streets it would be optimal for the deployment while historical statistics is a good step, we believe IoT would increase efficiency in traffic law enforcement and also provide a real-time feed to the traffic management control system.
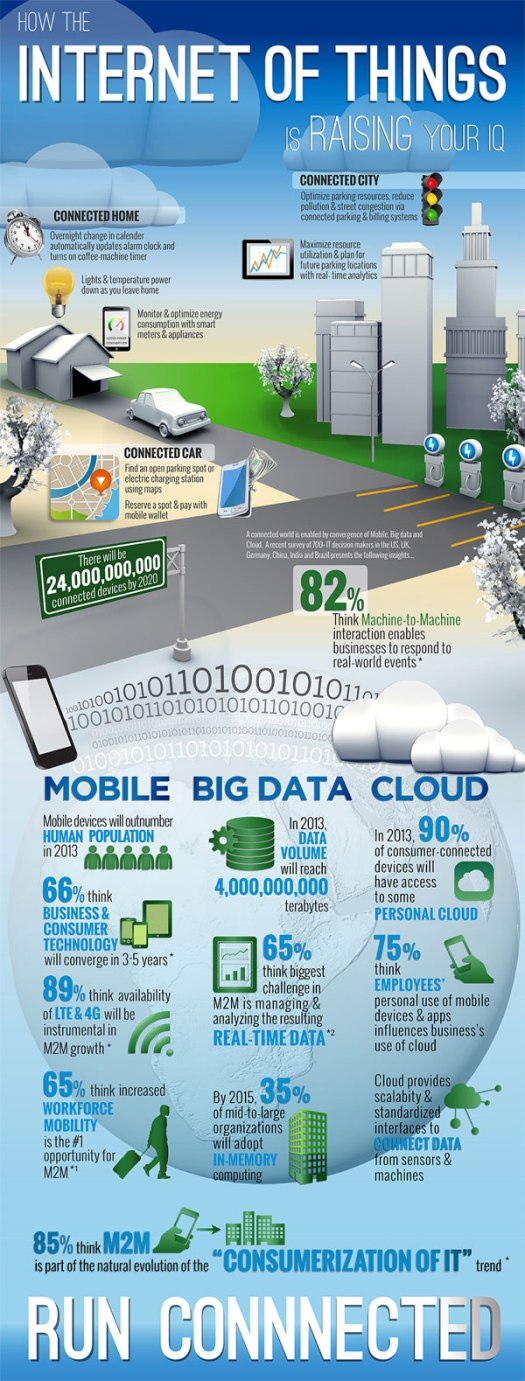
The Internet of things (IoT) is a new paradigm that describes all objects which are equipped with micro controllers, transceivers and a secure communication protocol to communicate with each other and the users (Zanella et al. 2014). IoT has much potential in many industrial sectors, and for personal, examples of IoT benefits are Health monitoring, home Automation, smart power grids and many other fields. In Smart Cities, the primary focus is to manage Traffic and resolve congestion, but that does not mean that IoT can be used to enforce traffic law by keeping cost down and increasing efficiency.
The proposed system consists of a small IoT device with an embedded radar module
The proposed system consists of a small IoT device with an embedded radar module. The device will provide car counting and classification data in real-time which will be transmitted over a low-speed internet bandwidth connection (Edge/3G ); and sent back to a data processing center, where data is logged and analyzed using Big-Data analysis software and also used to train a learning model( A.I. Expert System) which later on can provide feedback to scheduling supervisors about which location is best for deployment.
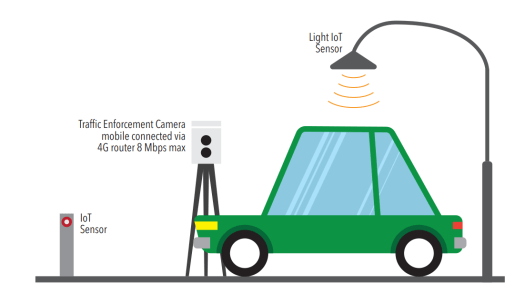
Figure 2. An Abstract Diagram of the Proposed Concept
Also, the collected data can be mined in real-time to provide congestion detection, road statistics and accident detection with decent accuracy that allow TMC (Traffic Management Center) operators to make an intelligent decision about routing traffic to different roads or provide feedback to drivers.
The traffic information is an essential source of data in smart cities which when applied to a proper analysis it can benefit both residents and the government. While residents can use this information to plan their schedule by factoring in the arrival times at their destinations. Governments can monitor the traffic congestion in the smart city in real-time, with fewer resource and in the much efficient way.
While vision based car counting & classification systems are already available in many cities, they require higher bandwidth connections, and they also need a much powerful hardware capable of doing image processing which is not the case in IoT (Talari et al. 2017). Also, the real value comes from mining the data.

Figure 3. the Benefits to the Value Chain Vs. The Level of Analytics (VITRIA, 2015)
The proposed system provides benefits by increasing efficiency in deploying the mobile unit which can increase collection and decrease required resource yielding to better profit margin.
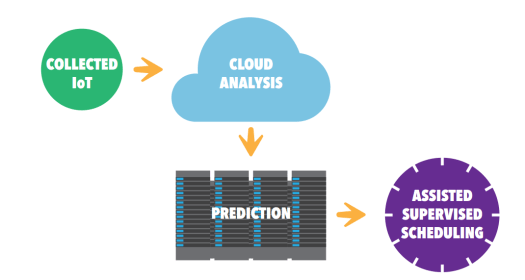 Figure 4. The Proposed Collection Process
Figure 4. The Proposed Collection Process
Figure 5. Dubai traffic violation processing (KHALEEJ TIMES, 2017)
References:
Talari, S., Shafie-khah, M., Siano, P., Loia, V., Tommasetti, A. and Catalão, J. (2017) ‘A Review of Smart Cities Based on the Internet of Things Concept,’ Energies, 10(4), 421.
VITRIA. 2015. Vitria’s Analytics Value Chain is The Key to Timely Outcomes in IoT [Online]. Available: http://www.vitria.com/vitrias-analytics-value-chain/ [Accessed 26 Aug 2017].
Zanella, A., Member, S., Bui, N., Castellani, A., Vangelista, L., Member, S. and Zorzi, M. (2014) ‘Internet of Things for Smart Cities,’ EEE INTERNET OF THINGS JOURNAL, 1, Pages 22-32.
19 die daily in KSA road accidents (2013) [online]. Available from: http://www.arabnews.com/news/464678 [accessed 25 August 2017].
5 violations other than speeding that Dubai Police radars catch, 2017. Youtube. Directed by KHALEEJ TIMES.